Automobiles Enter the “Age of Cyberattacks”: The Risks Brought by SDVs “Hijacking” Can Put Lives at Risk—Rock-Solid Security Is Required
- # Human Resource Development
- # Mobility DX

A Competition to Discover Specialized Talent: “VCC” Opens Its Doors to Students
VCC (Vehicle Cybersecurity Competition), described as the world’s largest contest for competing in knowledge and skills related to automotive CS, held its Japan tournament on October 3, 2025, in Minato City, Tokyo. It is organized by VicOne, a Trend Micro subsidiary known for “Virus Buster,” with the aim of cultivating the next generation of security talent and strengthening collaboration among diverse participants.

Nine teams participated. Over six and a half hours, they worked through 15 questions based on tasks developed by Toyota Motor researchers for security research and education. It is akin to a “mystery-solving puzzle” in the security field—participants use specialized knowledge and techniques to uncover hidden answers. It is far from straightforward, yet it also carries appeal and interest that go beyond being merely a technical contest. To broaden awareness among people from a wide range of backgrounds, this year the event opened participation not only to top teams from the global finals and automotive-related companies, but also to students. One participant, a second-year female student at the University of Nagasaki Prefecture, said, “I’ve been interested in security since high school. I thought I knew more than most people my age, but competing made me realize I was a ‘frog in a well.’ I want to keep improving.” Though she voiced frustration, her eyes shone with determination.

Max Cheng, CEO of VicOne, emphasized the significance of the competition: “With the advent of SDVs, vehicles will integrate with more external systems than ever. Convenience will rise, but so will risks. That is precisely why strengthening understanding of automotive security—and preparedness—will be indispensable.”
Mobility DX Strategy Makes Countermeasures a Core Pillar, Sounding the Alarm by Explicitly Citing Vulnerabilities
SDVs continuously generate new value by enhancing control functions online and adding content. At the same time, as Mr. Cheng noted, this also means SDVs come with dangers that conventional vehicles did not. If the servers connected to a vehicle are attacked, scenarios could include leakage of personal information, or services becoming unavailable due to malicious, massive data-processing requests. Users with low awareness may inadvertently use illegitimate apps and become infected with malware. There is also the possibility that unauthorized data affecting vehicle control could be sent via Wi-Fi, “hijacking” the vehicle. The list of conceivable risks is endless.
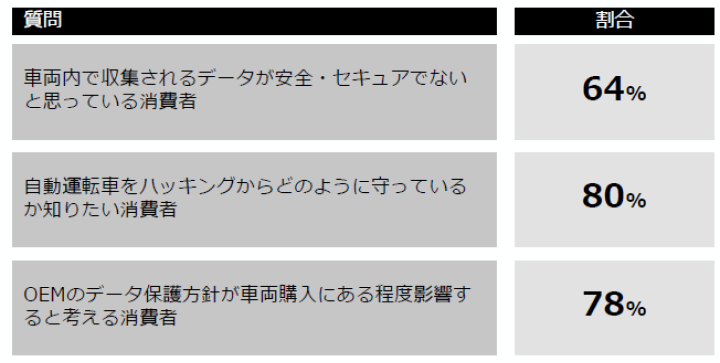
For this reason, the “Mobility DX Strategy” prominently positions security countermeasures. As a concrete SDV risk, it cites an example in which Keio University and the University of California found a vulnerability in part of a LiDAR sensor—used to determine the distance and shape of objects via lasers—in February 2025. They reportedly managed to invalidate pedestrian data from long range. The strategy also points out that in the future, security measures and privacy, together with safety and peace of mind, could become factors that differentiate vehicle value. It references a U.S. survey reporting that 78% of consumers believe OEM data-protection policies influence vehicle purchases to some extent.
Reflecting these realities, the strategy includes policies such as sharing vulnerability information within the industry and promoting talent development. As a means of information sharing, it highlights the “SBOM (Software Bill of Materials).” In Japanese, it is essentially a “parts list for software,” explicitly showing the various functions (components) embedded in software, their dependencies, and their sources. Much of today’s software is built from vast, complex combinations of components such as OSS (Open Source Software), making it a “black box” in which embedded risks are difficult to grasp. SBOMs increase software transparency, enabling a comprehensive view of threats and vulnerabilities.

ISAC, the Core of Automotive Security, Is Growing in Presence
J-Auto-ISAC plays a central role in automotive security initiatives, including SBOM-related efforts. ISACs are international organizations that analyze information on threats, vulnerabilities, and incidents and provide it to member companies, helping raise overall resilience against cyberattacks. In addition to the automotive sector, ISACs exist in fields such as finance, transportation, and electric power.
Masafumi Yamasaki, Center Director at the Cybersecurity Ecosystem Building Center within Auto-ISAC (and a section chief in Mazda’s MDI & IT division), said that “a certain level of safety can be ensured” in addressing conceivable threats and vulnerabilities. Vehicle manufacturing and software updates are required to comply with UN regulations related to cybersecurity. Cars also run “real-time OSs (operating systems),” which demand reliable processing within limited time, and differ from general-purpose OSs (such as those on PCs) that have traditionally been targets of cyberattacks. For these reasons, it is said to be unlikely that cyberattacks will render vehicles uncontrollable.
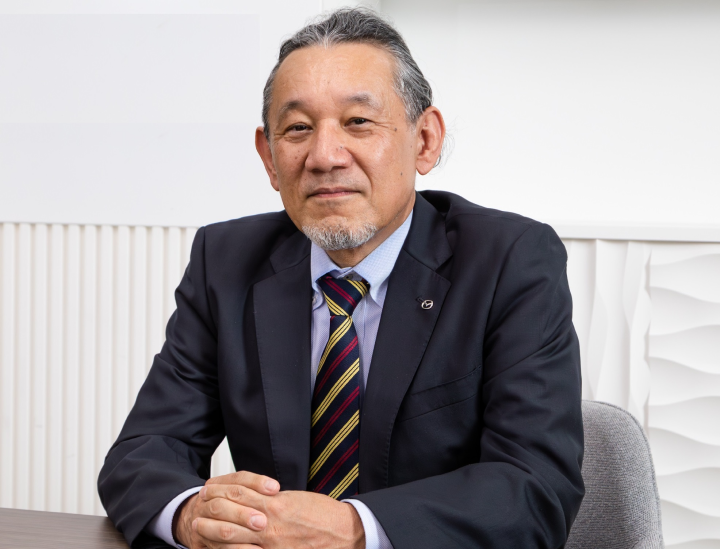
However, toward the full-fledged SDV era, he also warned, “I am concerned that software not properly assured for safety and security could be installed in vehicles, and that updates could expose us to cyberattacks we did not intend.” This is because components used in OSS, infotainment, and existing IT systems could be incorporated into automobiles in ways not intended by manufacturers.
The automotive supply chain spans a broad range of related companies and is hierarchical—from OEMs to parts suppliers, to their suppliers, and onward. For any single company to fully grasp the complete picture of the software being embedded is difficult in terms of both human workload and cost. In that sense, the role of ISAC—pushing forward SBOM development and talent development to fill the gaps—has become extremely important. Regarding human resources, Mr. Yamasaki noted that “approaches to security measures differ depending on where you are in the vehicle lifecycle, from development to post-sale services,” adding that they are “working in cooperation with industry organizations such as the Japan Automobile Manufacturers Association to create a skill map.”
“Building Momentum Through Commercialization and Cross-Industry Collaboration,” an Expert Says
What are the challenges of automotive security in the SDV era, and what is the significance of VCC? We spoke from a private-sector standpoint with Akinobu Oda, the head of VicOne Japan—a cybersecurity professional—about these questions.

“In the SDV era, automotive security is indispensable. Because personal information is aggregated in vehicles, there is a risk of leakage—and above all, if control systems are taken over, it can become a matter of life and death. The scope we must cover will expand beyond what we currently imagine.”
“However, consumers included, we have not reached a mindset where security measures are ‘as natural as turning a faucet and water coming out,’ like in existing IT. There are two major opportunities for momentum to grow: the development of relevant regulations, and real damage occurring due to cyberattacks—including serious accidents. But we cannot, as an industry, wait for the latter. If something happens first, it is too late, and it would only heighten distrust toward SDVs.”
“As the government also emphasizes, it is extremely important for the industry to collaborate beyond its boundaries and permeate consumers’ understanding of the value of automotive security. If that happens, the industry can ask for appropriate compensation in return for delivering that value. If this field takes shape as a business—and ultimately an industry—it will also contribute at a high level to social needs for safety and peace of mind.”
“In that sense, I hope VCC becomes an opportunity for participants—including students studying IT—to discover fields in which they can thrive that they did not previously know about, and to take an interest in automotive security. As the competition continues and awareness rises, new ‘seeds’ of talent will emerge. We have expertise cultivated at Trend Micro, our parent company, and elsewhere. We are confident that our role is to support the creation of value for security measures—just as the IT field has done. VCC, where collaboration with the automotive industry can be expected, is part of that effort.”
Related Articles
-
- # Collaborative Partnership
- # Mobility DX
2026.03.05
-
- # Human Resource Development
- # Mobility DX
2026.03.05
-
- # Collaborative Partnership
- # Mobility DX
2026.02.25
Other contents




